42 releases (25 breaking)
| 0.26.1 | Sep 14, 2024 |
|---|---|
| 0.26.0 | Sep 9, 2023 |
| 0.25.0 | Jan 28, 2023 |
| 0.24.3 | Nov 13, 2022 |
| 0.5.2 | Nov 26, 2018 |
#493 in Email
101 downloads per month
1MB
25K
SLoC
sn0int 





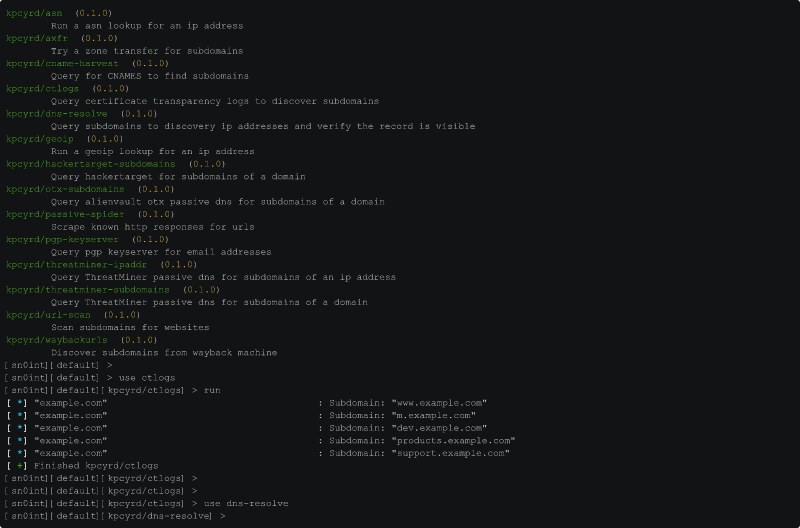
sn0int (pronounced /snoɪnt/) is a semi-automatic OSINT framework and
package manager. It's used by IT security professionals, bug bounty hunters,
law enforcement agencies and in security awareness trainings to gather
intelligence about a given target or about yourself. sn0int is enumerating
attack surface by semi-automatically processing public information and mapping
the results in a unified format for followup investigations.
Among other things, sn0int is currently able to:
- Harvest subdomains from certificate transparency logs and passive dns
- Mass resolve collected subdomains and scan for http or https services
- Enrich ip addresses with asn and geoip info
- Harvest emails from pgp keyservers and whois
- Discover compromised logins in breaches
- Find somebody's profiles across the internet
- Enumerate local networks with unique techniques like passive arp
- Gather information about phonenumbers
- Harvest activity and images from social media profiles
- Basic image processing
sn0int is heavily inspired by recon-ng and maltego, but remains more flexible and is fully opensource. None of the investigations listed above are hardcoded in the source, instead they are provided by modules that are executed in a sandbox. You can easily extend sn0int by writing your own modules and share them with other users by publishing them to the sn0int registry. This allows you to ship updates for your modules on your own instead of pull-requesting them into the sn0int codebase.
For questions and support join us on IRC: irc.hackint.org:6697/#sn0int
Installation
Archlinux
pacman -S sn0int
Mac OSX
brew install sn0int
Debian/Ubuntu/Kali
There are prebuilt packages signed by a debian maintainer:
sudo apt install curl sq
curl -sSf https://apt.vulns.sexy/kpcyrd.pgp | sq dearmor | sudo tee /etc/apt/trusted.gpg.d/apt-vulns-sexy.gpg > /dev/null
echo deb http://apt.vulns.sexy stable main | sudo tee /etc/apt/sources.list.d/apt-vulns-sexy.list
apt update
Docker
docker run --rm --init -it -v "$PWD/.cache:/cache" -v "$PWD/.data:/data" ghcr.io/kpcyrd/sn0int
Alpine
apk add sn0int
OpenBSD
pkg_add sn0int
Gentoo
layman -a pentoo
emerge --ask net-analyzer/sn0int
NixOS
nix-env -i sn0int
For everything else please have a look at the detailed list.
Getting started
- Installation
- Build from source
- Running your first investigation
- Autonoscope
- Writing your first module
- Database
- Structs
- Activity
- Notifications
- Keyring
- Configuration
- Sandbox
- Function reference
- asn_lookup
- base64_decode
- base64_encode
- base64_custom_decode
- base64_custom_encode
- base32_custom_decode
- base32_custom_encode
- clear_err
- create_blob
- datetime
- db_add
- db_add_ttl
- db_activity
- db_select
- db_update
- dns
- error
- geoip_lookup
- hex
- hmac_md5
- hmac_sha1
- hmac_sha2_256
- hmac_sha2_512
- hmac_sha3_256
- hmac_sha3_512
- html_select
- html_select_list
- http_mksession
- http_request
- http_send
- http_fetch
- http_fetch_json
- img_load
- img_exif
- img_ahash
- img_dhash
- img_phash
- img_nudity
- info
- intval
- json_decode
- json_decode_stream
- json_encode
- key_trunc_pad
- keyring
- last_err
- md5
- mqtt_connect
- mqtt_subscribe
- mqtt_recv
- mqtt_ping
- pgp_pubkey
- pgp_pubkey_armored
- psl_domain_from_dns_name
- ratelimit_throttle
- regex_find
- regex_find_all
- semver_match
- set_err
- sha1
- sha2_256
- sha2_512
- sha3_256
- sha3_512
- sleep
- sn0int_time
- sn0int_time_from
- sn0int_version
- sock_connect
- sock_upgrade_tls
- sock_options
- sock_send
- sock_recv
- sock_sendline
- sock_recvline
- sock_recvall
- sock_recvline_contains
- sock_recvline_regex
- sock_recvn
- sock_recvuntil
- sock_sendafter
- sock_newline
- sodium_secretbox_open
- status
- stdin_readline
- stdin_read_to_end
- str_find
- str_replace
- strftime
- strptime
- strval
- time_unix
- url_decode
- url_encode
- url_escape
- url_join
- url_parse
- url_unescape
- utf8_decode
- warn
- warn_once
- ws_connect
- ws_options
- ws_recv_text
- ws_recv_binary
- ws_recv_json
- ws_send_text
- ws_send_binary
- ws_send_json
- x509_parse_pem
- xml_decode
- xml_named
Rationale
This tool was written for companies to help them understand their attack surface from a blackbox point of view. It's often difficult to understand that something is easier to discover than some people assume, putting them at risk of false security.
It's also designed to be useful for red team assessments and bug bounties, which also help companies to identify weaknesses that could result in a compromise.
Some functionality was written to do the same thing for individuals to raise awareness about personal attack surface, privacy and how much data is publicly available. These issues are often out of scope in bug bounties and sometimes by design. We believe that blaming the user is the wrong approach and these issues should be addressed at the root cause by the people designing those systems.
License
GPLv3+
Dependencies
~110MB
~2M SLoC